i-Guard : Advanced Monitoring Solutions for Complete Asset Protection
i-Guard: in summary
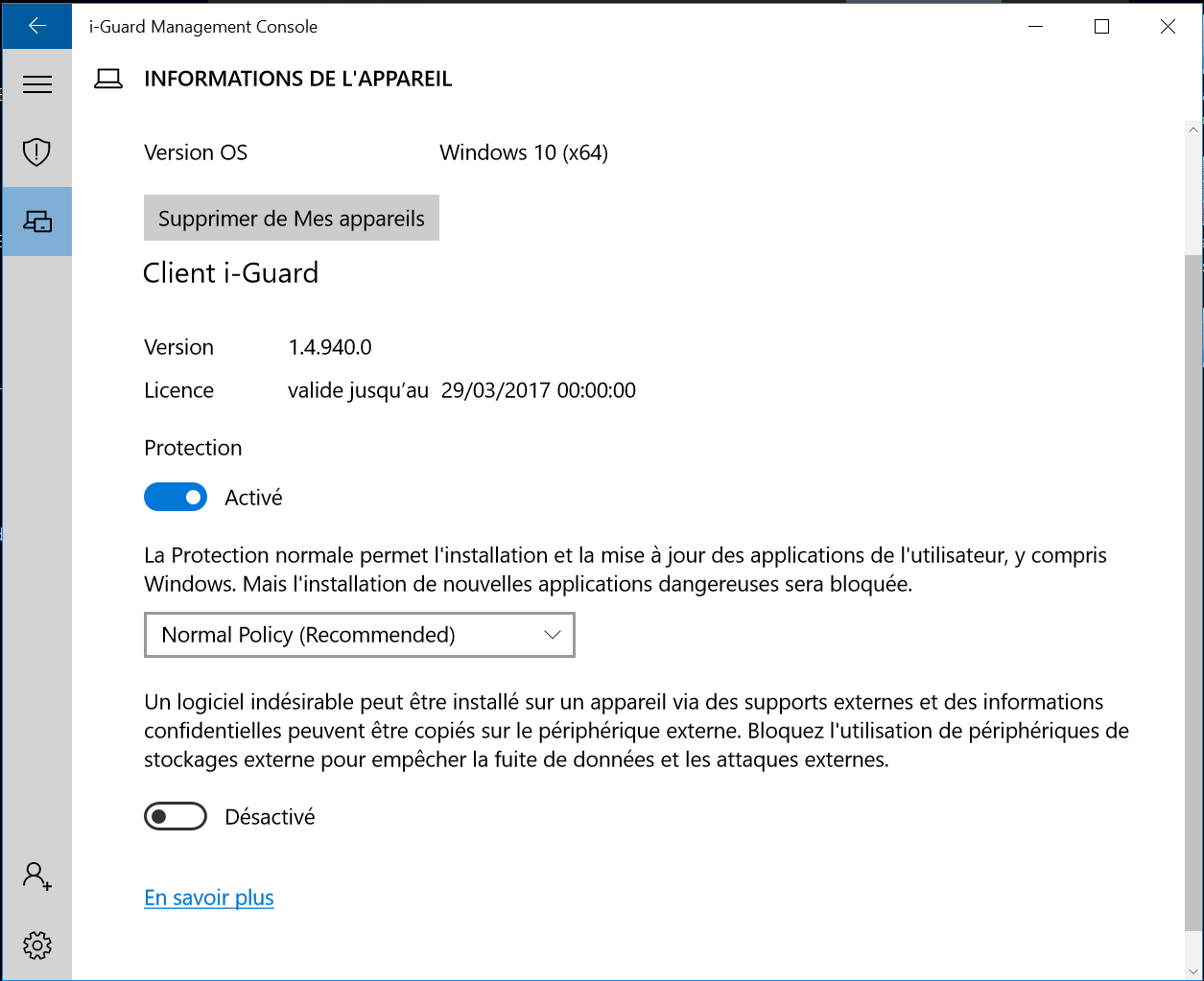
i-Guard offers robust monitoring and control solutions designed for businesses needing heavy-duty asset protection and operational oversight. Targeted at companies handling critical infrastructure, i-Guard stands out with its real-time alert system, detailed asset tracking, and seamless integration capabilities.
What are the main features of i-Guard?
Real-Time Alerts and Notifications
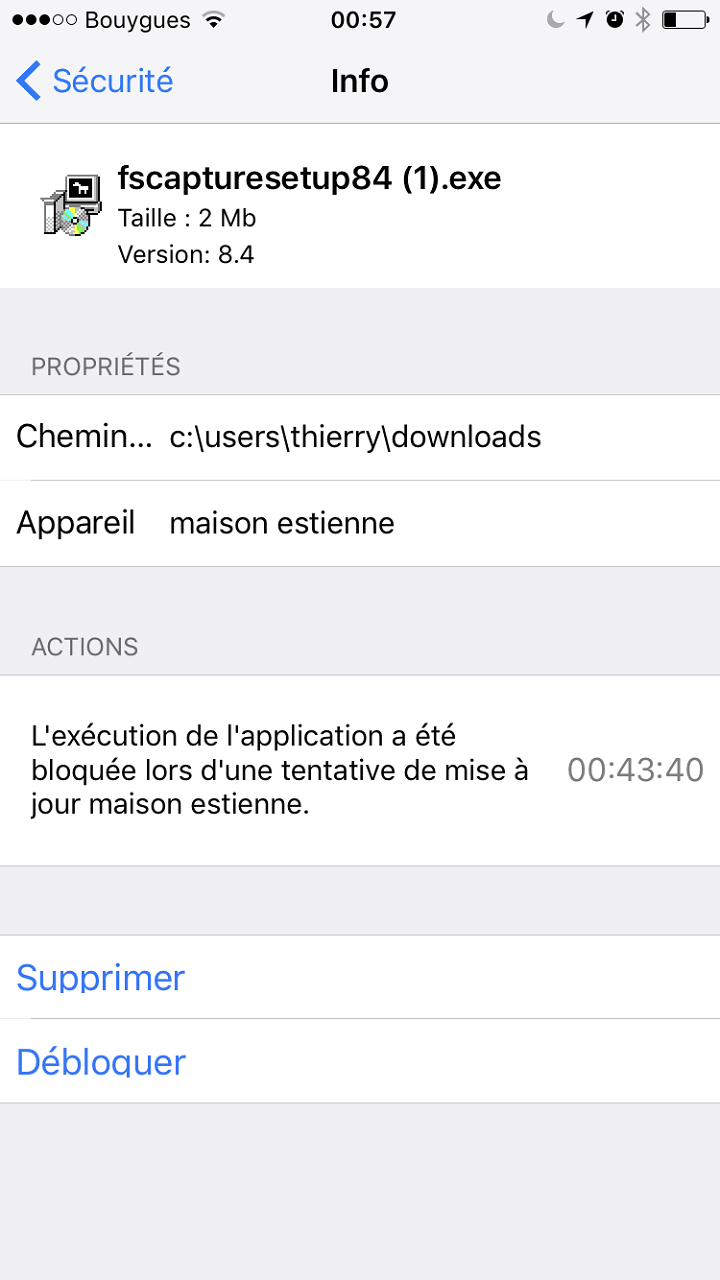
One of the most compelling features of i-Guard is its real-time alert system designed to keep you updated on the status of your assets constantly.
- Instant notifications: Receive immediate alerts on abnormalities or potential issues.
- Custom thresholds: Configure specific conditions that trigger notifications.
- Multiple channels: Get alerts via SMS, email, and mobile app.
Detailed Asset Tracking
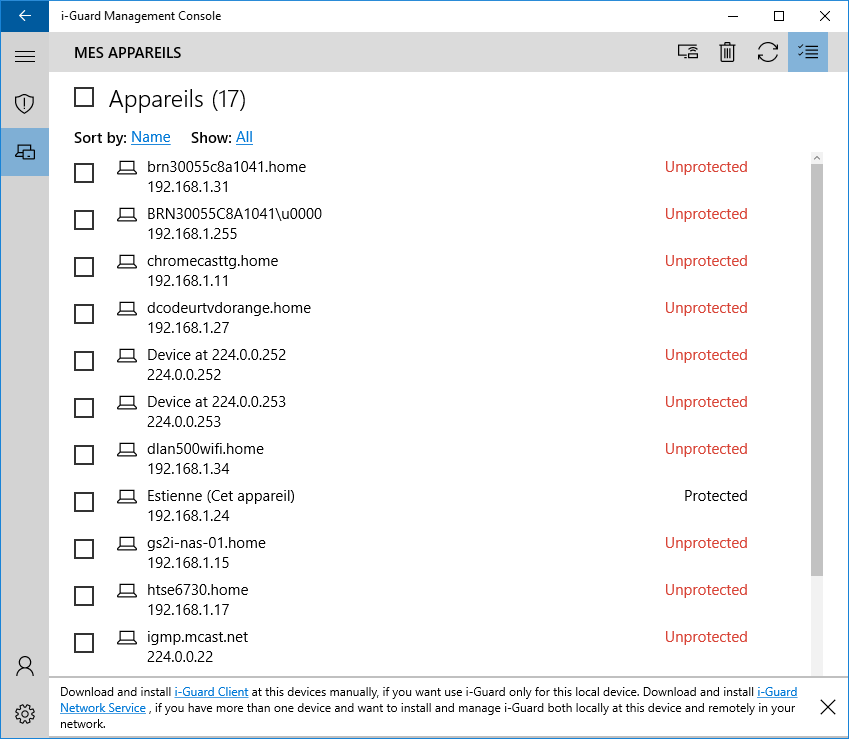
i-Guard provides comprehensive asset tracking to ensure all assets are monitored systematically.
- Location tracking: Keep track of the geographical position of all assets in real-time.
- Status monitoring: Get detailed information on the operational status and performance metrics.
- History logs: Access historical data and generate reports for analysis purposes.
Integration Capabilities
i-Guard is built with flexibility in mind, offering seamless integration options to enhance functionality.
- API integrations: Easily connect i-Guard with other third-party software platforms.
- IoT compatibility: Integrate with various IoT devices for enhanced monitoring.
- Scalability: Scale the software features up or down based on business requirements.
i-Guard: its rates
Standard
Rate
On demand
Standard
Rate
On demand
Clients alternatives to i-Guard

Advanced antivirus software with real-time protection, anti-phishing, anti-fraud, anti-spam, and anti-ransomware capabilities.
See more details See less details
Bitdefender's antivirus software provides a comprehensive, all-in-one solution for protecting your devices against a wide range of threats. Its advanced features include real-time protection against malware, phishing, fraud, spam, and ransomware, ensuring that your data and privacy remain safe at all times.
Read our analysis about GravityZone by BitdefenderBenefits of GravityZone by Bitdefender
Enterprise-level protection built for small businesses
Fast setup with no server or tech skills needed
Cloud-based console to manage all devices remotely

Protect your device from malware, viruses and phishing attacks with this powerful antivirus software. Enjoy real-time protection and automatic updates.
See more details See less details
Surfshark Antivirus offers a user-friendly interface and a range of customizable settings to suit your needs. Its advanced threat detection technology ensures that your device is always secure, while its light footprint ensures that it won't slow down your system. With 24/7 customer support, you can trust that your device is in safe hands.
Read our analysis about Surfshark Antivirus
Protect your devices with a powerful antivirus software. Secure your data and prevent cyber attacks with ease.
See more details See less details
RG System Endpoint Security offers advanced protection against malware, ransomware, and other cyber threats. With real-time monitoring and automatic updates, you can trust that your devices are always secure. Plus, the software is easy to use and customizable to fit your specific needs.
Read our analysis about CybersécuritéBenefits of Cybersécurité
Full SaaS
Bitdefender reference solution
Windows, Linux and Mac agent
Appvizer Community Reviews (0) The reviews left on Appvizer are verified by our team to ensure the authenticity of their submitters.
Write a review No reviews, be the first to submit yours.